I had the honor and pleasure of being asked to teach a four hour incident response class at last month’s Circle City Con in Indianapolis, IN (you can watch a recording, here). The subject was preestablished based on attendee interest: building an incident response program in small, medium, and large enterprises. Granted, most of the talks I give aren’t on spaceships or robots or other such entertaining stuff, but this in particular presented a conundrum – developing a program and team can be a spectacularly dry subject.
I approached the class with a few goals in mind:
1) I wanted to ensure I kept audience interest for the full four hours, (and maintained my ability to speak!)
2) I wanted to ensure every critical topic about building a team I presented was reinforced in an entertaining way.
and finally,
3) Maintaining audience involvement so that they would be offered auditory, visual, and hands on learning simultaneously, giving them the best chance of success possible.
The answer became obvious – I firmly believe that incident response is made of endless, great stories. Therefore, I would gamify building an incident response team, turning it into a story-based role playing game. I’d already had positive exposure to gamification in and out of infosec education – I regularly speak at gaming conventions about hacking. Now it was apparent that I was going to have to bring gaming to the hacking convention.
Gamification has been a key component of education for a long time, but it in the past it’s been pretty kid-specific. However, as gaming itself becomes more mainstream, teens and adults are becoming more and more comfortable in thinking of their lives in terms of games – accumulating achievements, reaching rewards through set goals, and learning through creative, fun activities. This has been reflected as the new, hot thing in everything from fitness apps to HR training – educators have discovered that people can often learn better and be more interested in fun, creative, and achievement-oriented environments.
The tremendous value gamification (and role playing in specific) brings to education is the creativity and emotional involvement it inspires. If I simply presented a case and explained my response, there’d be no emotional weight – the students would be passive observers hearing about something that already happened. I could take it a step further and give each group a pre-written scenario – a vast improvement because they would have to think critically about their solution. However, my solution took this emotional involvement a bit further, letting each group randomly generate their own unique scenario, with random benefits and pitfalls. I couldn’t predict the outcome, therefore every situation was unique and posed it’s own challenges (to the class, and to me).
After 40 minutes of lecture where I presented incident response team concepts and methodology, I let each of my student groups generate a company faced with multiple security problems. Each team was given two polyhedral dice (20 and 6 sided). They were provided some brief instructions:
Exercise 1: Our Saga Begins Building an Incident Response Team
INSTRUCTIONS: You will be completing these exercises as a small group. Every group’s scenario will be a
little different based on the roll of the polyhedral dice you’ve been provided. Fill in the blanks with your
random dice roll, and then complete the exercises. Some groups will be ‘luckier’ than others, but that’s how the cookie crumbles. Every group will share their situation and solution.
And some static background, for the sake of brevity:
Due to your stellar reputation in Incident Response, your consulting firm has been hired by Renraku, a
4500 employee global company, to design their very first dedicated Incident Response team. They’ve
been having an increasing number of security incidents over the past year and they’ve relied on outside
contractors and vendors to help investigate and resolve them. They currently only have a Security
Operations Center (SOC) that does some basic log monitoring, patching, and malware remediation. The
CISO Mr. Lanier provides the following specifications:– The IR team will respond 24/7/365 with a projected staff of 10 people (on an on-call rotation).
– They will respond to physical and digital security incidents
– IR team will collaborate with members of the HR, legal, loss prevention, and physical security teams.
– On detection of incidents, the SOC will normally be the ones to page out the Incident Response team.
I then let them roll the dice to determine some key aspects of the incident response scenario:
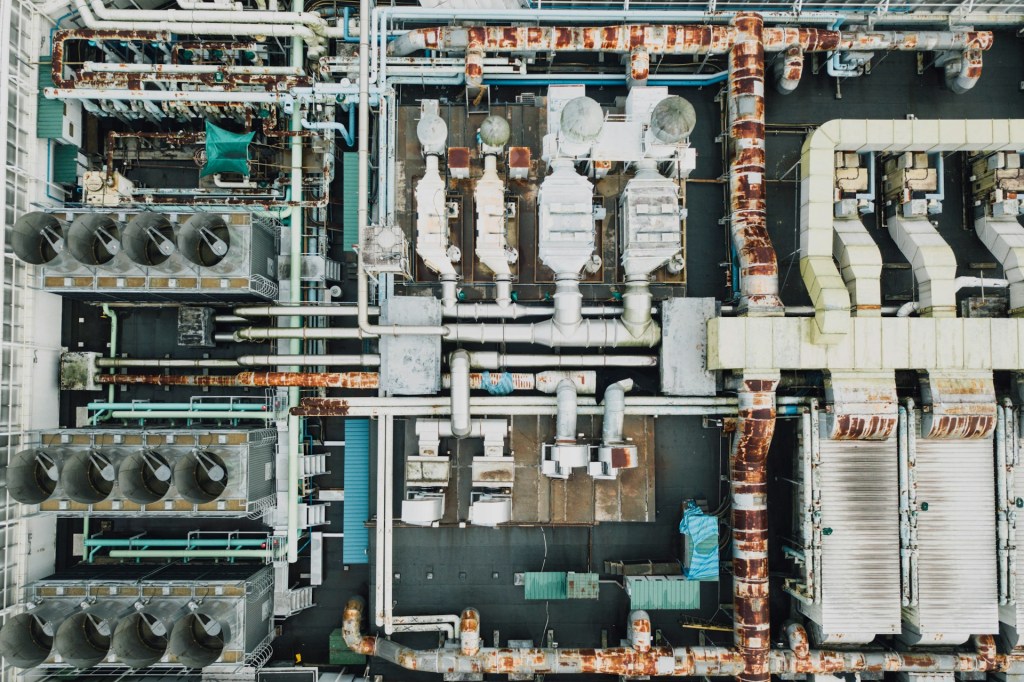
Roll [D6] _______. This will reflect the industry that Renraku focuses on (for the rest of this course):
(1) Retail Stores
(2) Hospitals
(3) Financial Investments
(4) Defense Contracting
(5) News Media
(6) Oil, Gas, and ElectricRoll [D20] ___________. This is how many major security incidents Renraku has been faced with in the
12 months. If you rolled over a 12, it means they were dealing with more than one incident at once (and
may have to again).Roll [D20] ___________. The number of months it took Renraku to detect their last major compromise.
Roll [D20] ___________. The number of countries that Renraku operates offices in.
Roll [D20] ___________. The number of subsidiaries with different system configurations and software
that have unrestricted connections to Renraku’s internal network.
This posed an interesting challenge because not everybody in the class had played a roleplaying game with polyhedral dice, before. Having small groups helped with this, as the people who enjoyed tabletop gaming immediately latched on and took their dice rolls very seriously!
I knew there would be stumbling points in presenting the course, and did my best to anticipate them. I predicted that some teams would be in very good situations and others in very untenable ones, so I was very careful to weight each dice roll to keep them in realistic ranges. In practice, this worked fairly well, but in the future I will be widening this range slightly because none of the groups were in a truly difficult staffing position on their mock incident response teams. I was also worried that some of the companies would turn out too identical, but fortunately my statistical math was (surprisingly) good and of my seven groups, only two ended up very similar in industry and security issues. This is something to consider carefully when developing a new scenario: what are the worst and best case scenarios that can occur?
The biggest issue I ran into ended up being time. This was both a bad and a good problem to have – the groups had in depth, occasionally heated discussions about their companies. I was trying to engage them emotionally and I think I succeeded to an extent because of this. I actually had to stop a couple of the exercises early to stay near the timeframes I had set for each exercise. In the future, I’ll be trimming down lecture a bit more and making the exercise constraints more clear. I stated at the beginning of the course that none of the exercises solutions needed to be technical in nature, but some of the groups worked out very interesting technical solutions to the problems.
Another problem I faced was rewarding achievement. When I present this course again, I’ll have to clearly establish criteria for which group wins each exercise (and wins fantastic geeky swag)! All of the groups had great solutions and creative ideas, and I felt very on-the-spot trying to choose a winner quickly.
During the class I learned very quickly that camping it up and interjecting roleplay kept it fun. I played the role of ‘GM’ throughout the exercises, occasionally rolling a D20 to see if the companies were set up in hostile countries or involved in embarrassing data breaches. I was careful to start this with groups that were already having a good time and playing with the scenario – the group that rolled miserably on their Oil & Gas company network and made up a great story as to why was repeatedly dogged by hacktivists! This really kept me on my toes. My recommendation to others less familiar with off-the-cuff roleplaying might be to write down some injects in advance.
All in all, I highly recommend this method for teaching the creative thinking and logical reasoning skills that are so desperately needed in incident response. Presenting a randomized scenario made each team care a bit more about the company they were representing, and introduced a large number of unpredictable scenarios. My students were engaged throughout the class and I got some very positive feedback afterwards.
I’m excited to continue development of my gamified Incident Response course through the year, and I’m happy to present it at cons as I’m available, or help you set up your own program. You can find my slides, worksheets, and sample scenarios on Google Docs here – I only ask for credit if you use my work directly. Enjoy!




Leave a comment